Introduction
As part of enhancing the Prancer Penetration Testing as Code (PAC) framework, a new flow called "Reachability Test" will be introduced. This feature aims to test if the target is reachable before initiating the scanning process. Utilizing the nmap functionality, this test will assess whether the target is up and running and determine the open ports on the target. Based on the results, the PAC CLI will report back to the commander, update the PAC Config file, and load relevant custom attacks accordingly.
Attack Surface Assessment Flow
After PAC CLI receives the PAC Config file and before starting the scanning, the Reachability Test will be initiated.
The Attack Surface Assessment will leverage the nmap functionality to check if the target is up and running, and determine which ports are open.
Based on the test results, the following actions will be taken: a. If the target is not up and running, the scanning process will be halted, and the PAC CLI will report back to the commander that the host is not reachable. Consequently, no results will be produced. b. If the target is running, the open ports will be mapped to their default service providers (e.g., port 22 for SSH) and tagged in the PAC Config file. When the PAC CLI loads custom attacks, it will consider these tags and load all relevant custom attacks.
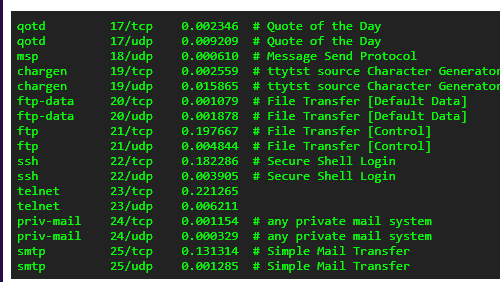
Use nmap-services for service tags. Typical excerpt from file looks like below. Based on the service, scope the PAC usecases.
By implementing the Attack Surface Assessment feature, the Prancer Penetration Testing as Code framework will be more efficient in determining if a target is reachable before initiating the scanning process. This enhancement will enable the framework to conserve resources, optimize the scanning process, and provide more accurate results to the end-users.
#!/bin/bash
# Check if an IP address is provided as an argument
if [ -z "$1" ]; then
echo "Usage: $0 <public-ip-address>"
exit 1
fi
IP_ADDRESS="$1"
OUTPUT_FILE="scan_results_$IP_ADDRESS.txt"
# Perform Nmap scan on the provided IP address
nmap -p 1-65535 -sV -sC -O -oN "$OUTPUT_FILE" "$IP_ADDRESS"
# Parse the results to determine if any open services are found
OPEN_PORTS=$(grep -E "open|filtered" "$OUTPUT_FILE" | wc -l)
if [ $OPEN_PORTS -gt 0 ]; then
echo "The virtual machine at $IP_ADDRESS is exposed."
echo "Evidence can be found in the file $OUTPUT_FILE."
else
echo "No exposed services were found on the virtual machine at $IP_ADDRESS."
fi