PAC Configuration Wizard for Azure Cloud
Introduction
Prancer Cloud Security Solution's Cloud Security Posture Management (CSPM) functionality provides an automated way to identify and remediate security risks in cloud environments. With the ability to scan a wide range of your Azure cloud resources, the CSPM engine integrated to the Prancer platform can identify misconfigurations, vulnerabilities, and compliance issues that may pose a risk to your environment. The findings are then presented in a well-defined report page, making it easy for security teams to quickly take action and improve the overall security posture of your Azure cloud environment.
This page describes how organizations can use their existing Azure account to run a penetration testing instance, with PAC generating a manifest file based on YAML format that provides all the details of the pentesting job, including the application information, scanner setup, target selection, and authentication configuration. Prancer PAC engine then communicates with your Azure tenant, creates the PAC scanner based on the configuration details, completes the pentesting scan, and displays the results on the "Pentest Findings" page.
** In order to conduct this process, click on the "Pentest Wizard" from the side menu and follow these instructions. **
Step 1 - Establish the connection to your Azure tenant
Select the "Azure Cloud" from the target environment selection. You can use either an existing connection available for you or create a brand new connection to the Azure tenant.
Select the "Existing connection" and search for your connection in the box to use one of the existing connections. To create a new connection, click on the "New connection" button. You need to fill out a few items to connect to your Azure tenant.
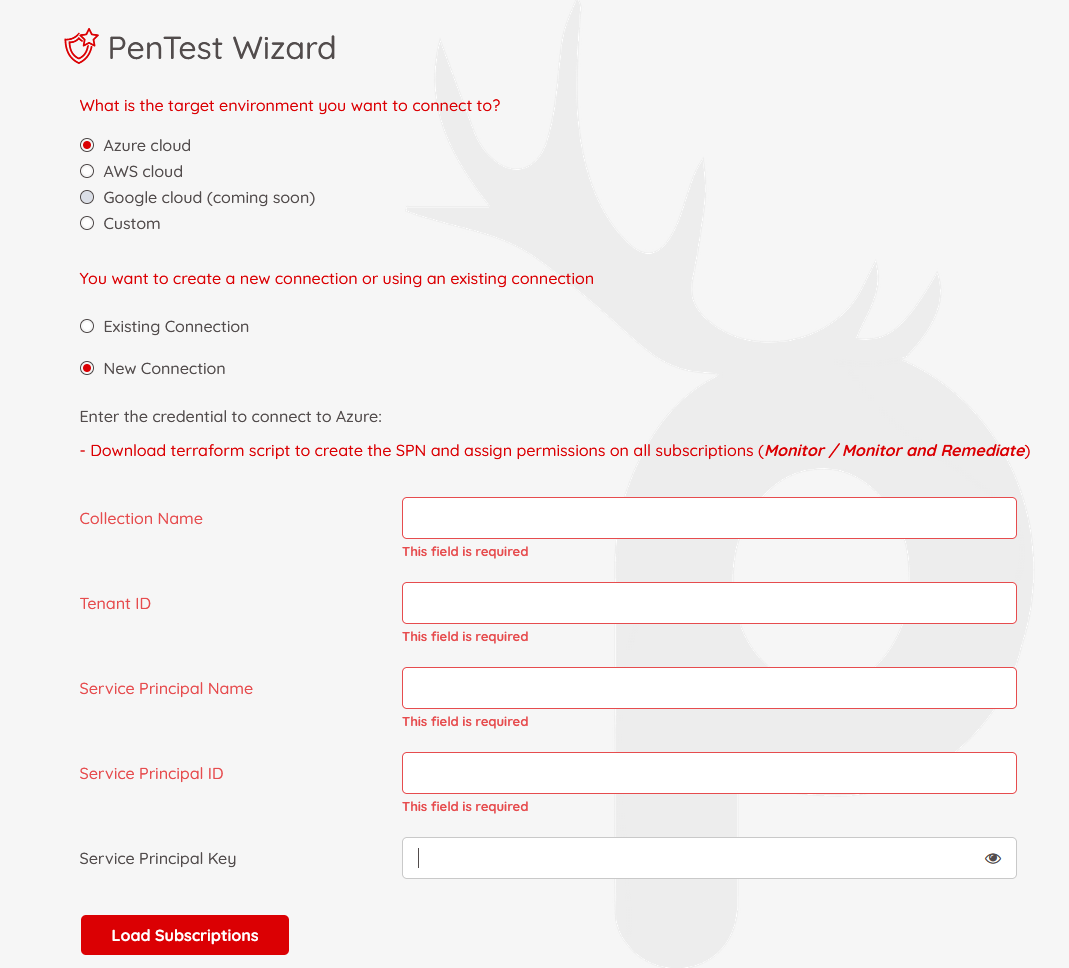
Prancer uses Service Principal Name (SPN) to connect to the Azure tenant. To understand more, check this link from Microsoft.
Collection Name: name of the collection you want to use for your Pentesting project. It will be used as an identifier for future use.
Tenant ID: Your Azure tenant ID
Service Principal Name: the name of the Service Principal
Service Principal ID: The Application ID of the Service Principal Account
Service Principal Key: Service Principal Secret
Permissions: The SPN account should have the proper permission on the subscription to read the resources and to be able to create pentest-related resources.
These are our recommendations for the SPN permission to use in PAC:
-
Read permission on the subscription: SPN can read the name of the resource groups and key vaults that hold authenticated scans' secrets. Also, for Internal Pentest scans, we need to read the information of vnet / subnets
-
Read permission on Keyvault Secrets: If you want to do an authenticated scan, you need to keep the secrets in an Azure key vault. the SPN account should have permission to read the secrets out of those specific key vaults. based on the type of the Keyvault RBAC configuration, you need to give the SPN the proper permission.
-
Permission to create resources: during the pentest in Azure, Prancer creates an Azure Container Instance (ACI) to hold the pentest scanner.
-
Permission on Azure Active Directory: IF you want to use the auto-discovery feature of Azure App registrations and Azure Enterprise Applications, the SPN should have the proper permission on Azure Active Directory.
-
Read Permission on Azure Resources: If you want to use the auto-discovery feature of PAC to find out the resources automatically in Azure and do a white box scan for you, you need to give the proper permission to the SPN account.
When you fill out the required information, click on the "Load Subscriptions" button to load all the subscriptions the SPN has access.
Select the subscriptions you want to include in your "Collection" and hit the Next button.
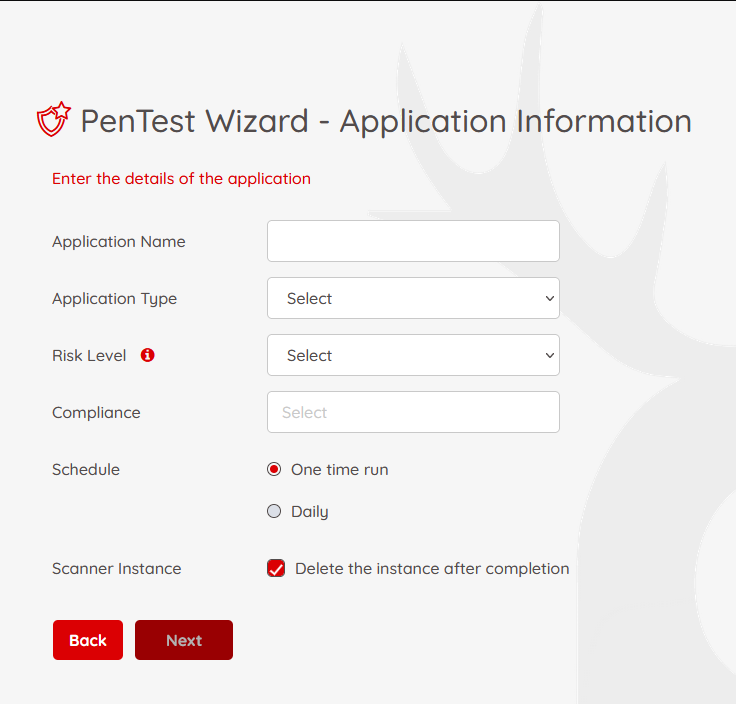
Step 2 - Application Information
On this page, we will fill out the basic information regarding the application you want to do the pentesting.
-
Application Name: give your application a name for future references
-
Application Type: PAC supports Web, Open API, and Soap API applications for scanning
-
Risk Level: There are three risk levels available for pentesting:
-
Safe: running pentesting rules which are safe for production instances.
-
Attack: When you run the pentesting in an attack mode, it will insert data into your forms. This is the best choice when you are pentesting on lower environments and have existing crawls.
-
Standard: doing safe and attack pentesting together. It is recommended for all lower environments.
-
-
Compliance: Which compliance do you have to follow. You can filter your applications based on the selected compliance later.
-
Schedule: How often do you want to run the pentesting? Is it just one time run? or you want to put it on a scheduled basis
-
Scanner Instance: What to do with the scanner instance when the Pentesting is completed in your environment?
- You have the option to stop the scanner
- You can delete that scanner completely
Note: PAC uses Azure Container Instances (ACI) to run pentesting. To understand more, check this link from Microsoft.
Step 3 - Scanner setup
You can use either an existing scanner from your Azure subscription or create a brand new scanner instance on the scanner setup page.
Option 1: Use Existing Scanner
To use an existing pentest instance, select the option on the page. Then you need to choose the Azure subscription, Region, Resource group, and the Scanner instance.
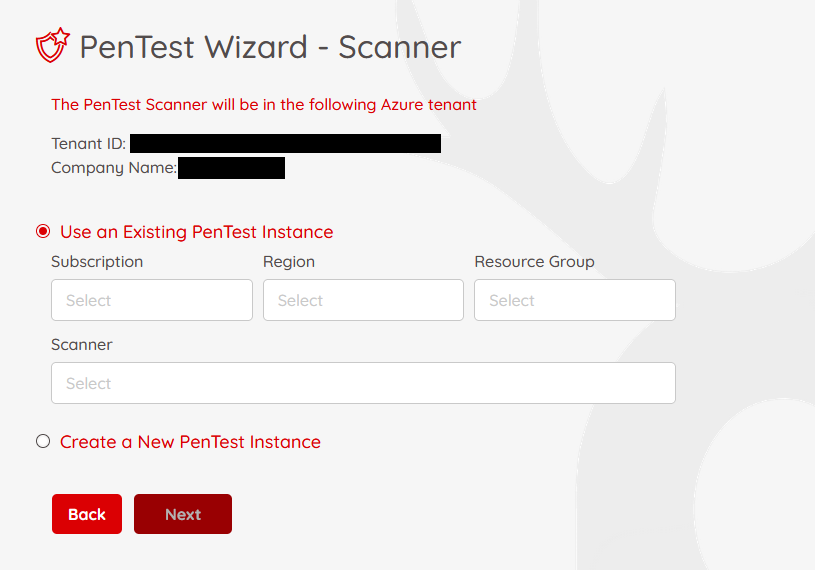
Note: The SPN account established the connection should have proper access to read Azure ACI instances.
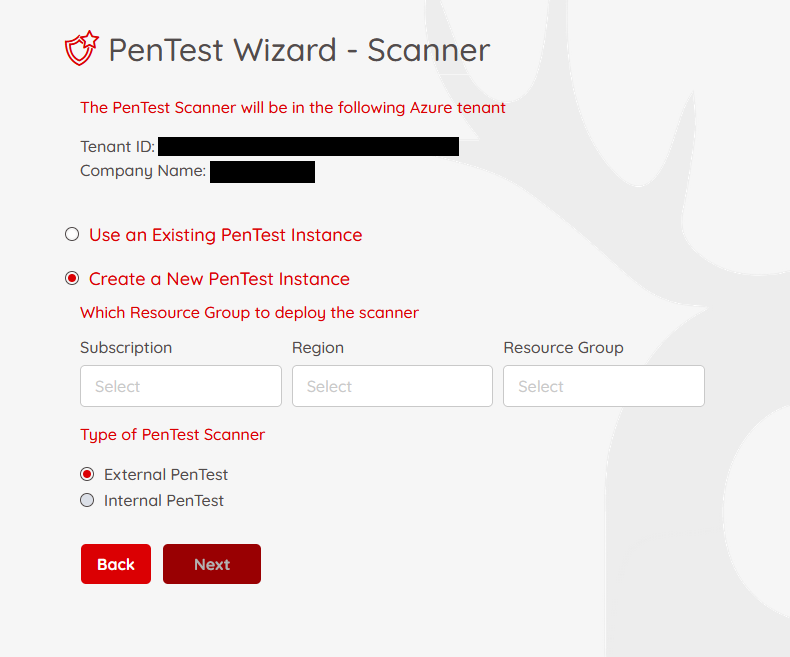
Option 2: Create New Scanner
To create a new pentest instance, select the appropriate item on the page, and enter the subscription name, Region, and Resource Group you want to put the scanner instance in.
Also, you have the option to do an External Pentest or an Internal Pentest.
-
When you are doing an External PenTest, it is supposed that your target is reachable from the internet. And Prancer PAC will spin up the ACI instance with a public IP address.
-
When doing an internal PenTest, you should select which subnet you want to put your scanner on. Your scanner won't have a public IP address and can do internal pentesting on resources resides on the selected subnet
Option 3: Use Prancer-Managed Scanner
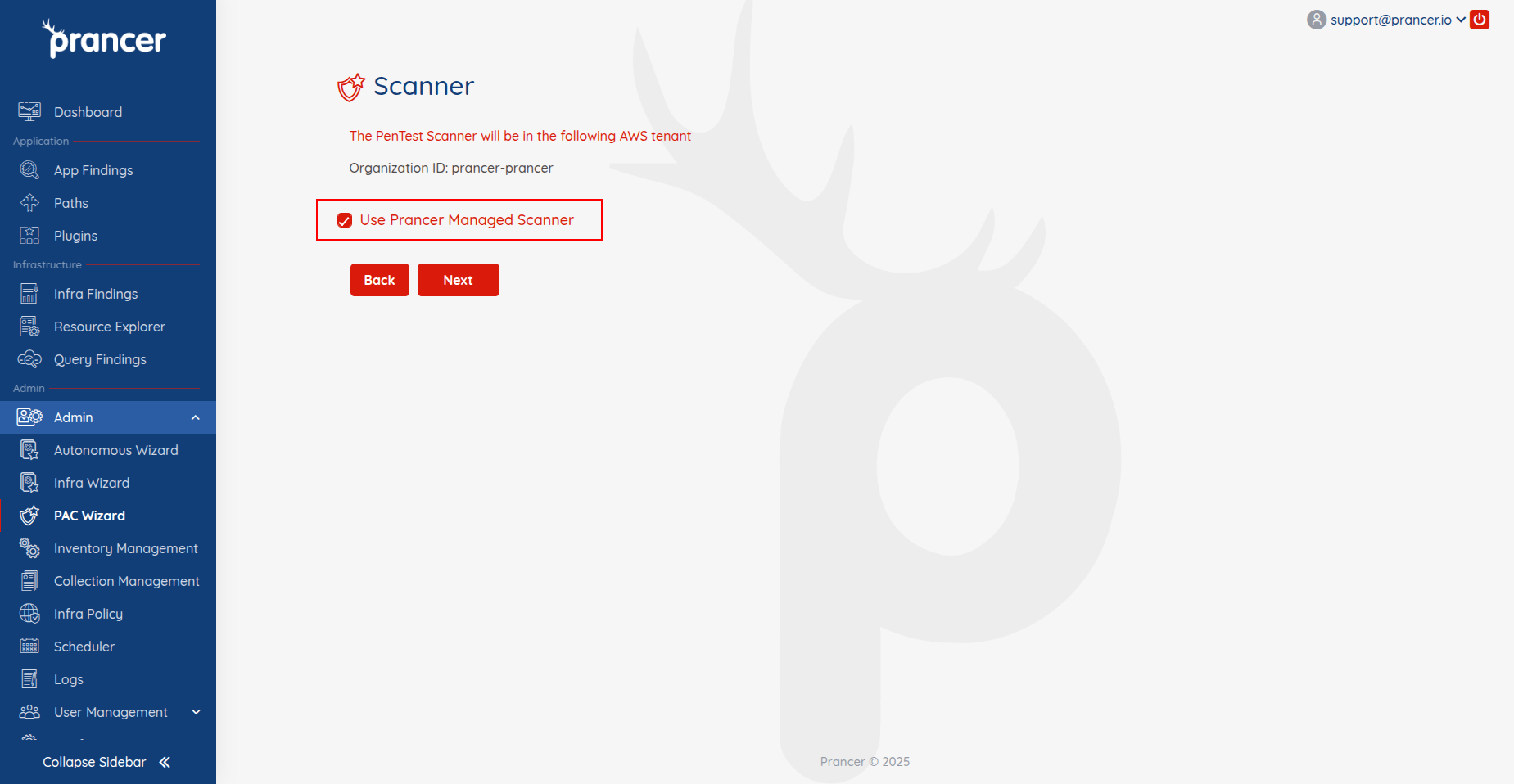
You can choose Prancer Managed Scanner, where Prancer handles creation and management of the scanner instance for you.
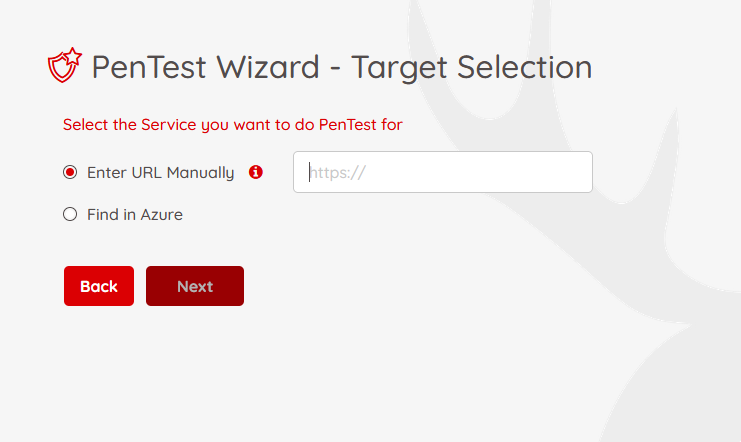
Step 4 - Target Selection
In this step, you will specify which target you want to run the pentest against. you have two options, you can either enter the URL endpoint manually or use the auto-discovery feature from Prancer's CSPM engine.
Note : If you want to use the auto-discovery feature of the Prancer's CSPM engine, make sure the SPN has proper access to the resources you want to do pentesting on.
To enter the endpoint manually, select the appropriate option on the page and enter the URL in the box. The server servicing the endpoint could be hosted on Azure (a virtual machine, an App Service, API Gateway, etc.) or outside the Azure as a publicly available endpoint.
You have the option to select the "Find in Azure" section to use the Prancer's CSPM engine and auto-discover the endpoints in Azure for you.
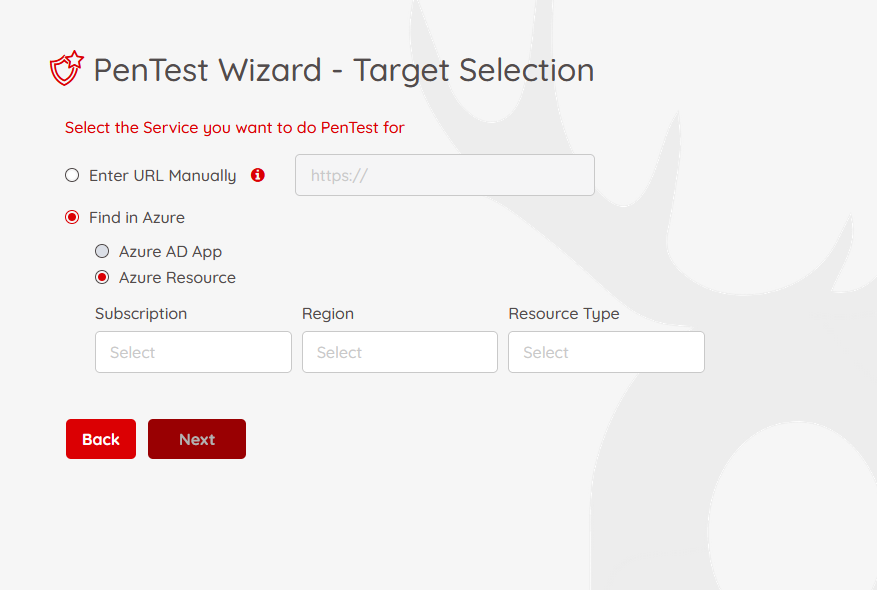
You can select Azure AD App to show all the available endpoints in Azure Active directory app registration, or select the "Azure resource" to find the specific type of resource in the Azure.
Enter the appropriate information on this page and hit "Next" button.
Step 5 - Authentication
On this page, you can configure the authentication information of your application.
Prancer PAC supports various authentication mechanisms, including:
-
Form-based
-
HTTP / NTLM
-
JSON-based
-
Azure AD
-
JWT Token
PAC requires different information to be entered on this page for each authentication type. All the secrets needed for the authentication are stored on the customer's tenant. PAC is not keeping any secret related to your application. As part of the authentication configuration, you need to select the vault based on the type of the Cloud and reference the secret items. For example, in the case of Microsoft Azure, we are using Azure Key Vault to retrieve the secrets at the time of pentesting.
** Azure Key Vault selection **
PAC uses a Key Vault in the customer's Azure tenant to retrieve secrets when doing pentesting. You need to specify which Key Vault holds the authentication secrets. To do that, You should select the subscription, Region, Resource Group and the name of the Key Vault.
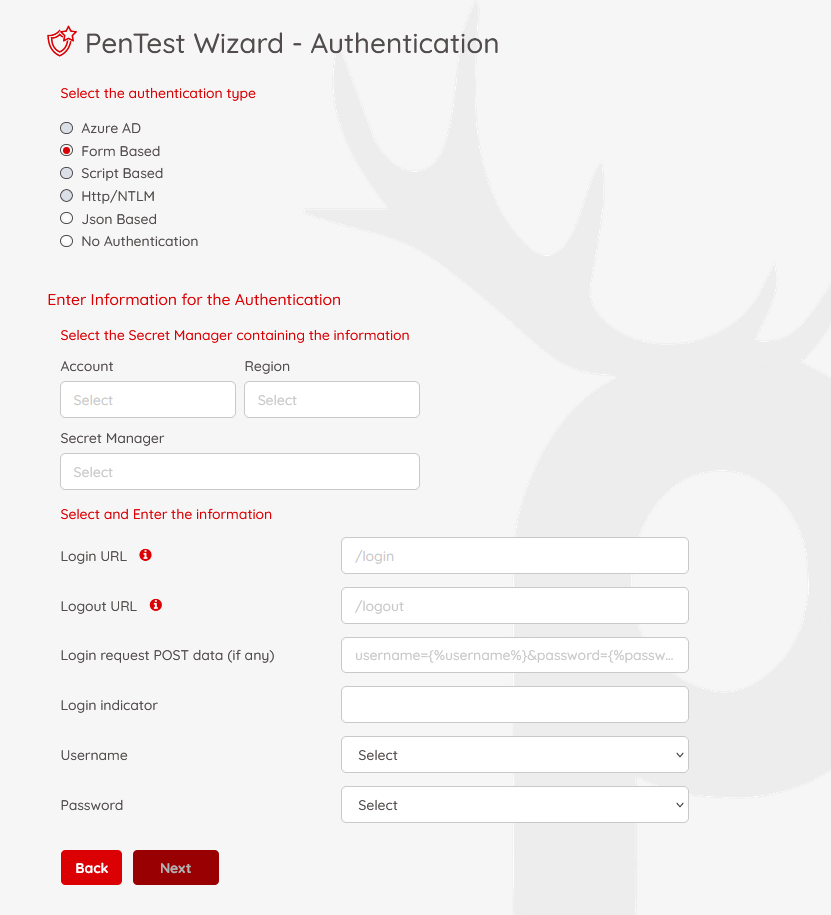
** Form-based Authentication **
Form-based authentication is a method most web applications use to authenticate their users. To configure PAC to use Form-based authentication, you should enter the following information:
-
Login URL: The URL of the login page in your web application. For example, "/login"
-
Logout URL: The URL of the logout page in your web application. For example, "/logout"
-
Login Request Post Data: The format of the post data you are using when submitting the login form. For example,
identity={%username%}&password={%password%}This means the variables developer used to send the post data back to the server areidentityandpasswordAt the time of pentesting, we are replacing{%username%}and{%password%}with the values we are retrieving from Azure Key Vault -
Login Indicator: When the user is logged in, what element on the page shows the user has logged in? For example, in all of your login pages, you have a logout link, which could indicate that a user is logged in.
-
Username: select the secret key from the Key Vault, which holds the username
-
Password: select the secret key from the Key Vault, which holds the password
-
When you have entered all the authentication information, click on "Next" button to go to the next page.
Step 6 - PAC file
In the last step of the pentesting wizard, PAC generates a manifest file based on the YAML format showing all the details you have entered in previous steps with more details. You can change the items here if you need. For example, for the name of the ACI scanner on the Azure, we have a default name "prancer-instances". You can change this name to something else to comply with your company's naming convention.
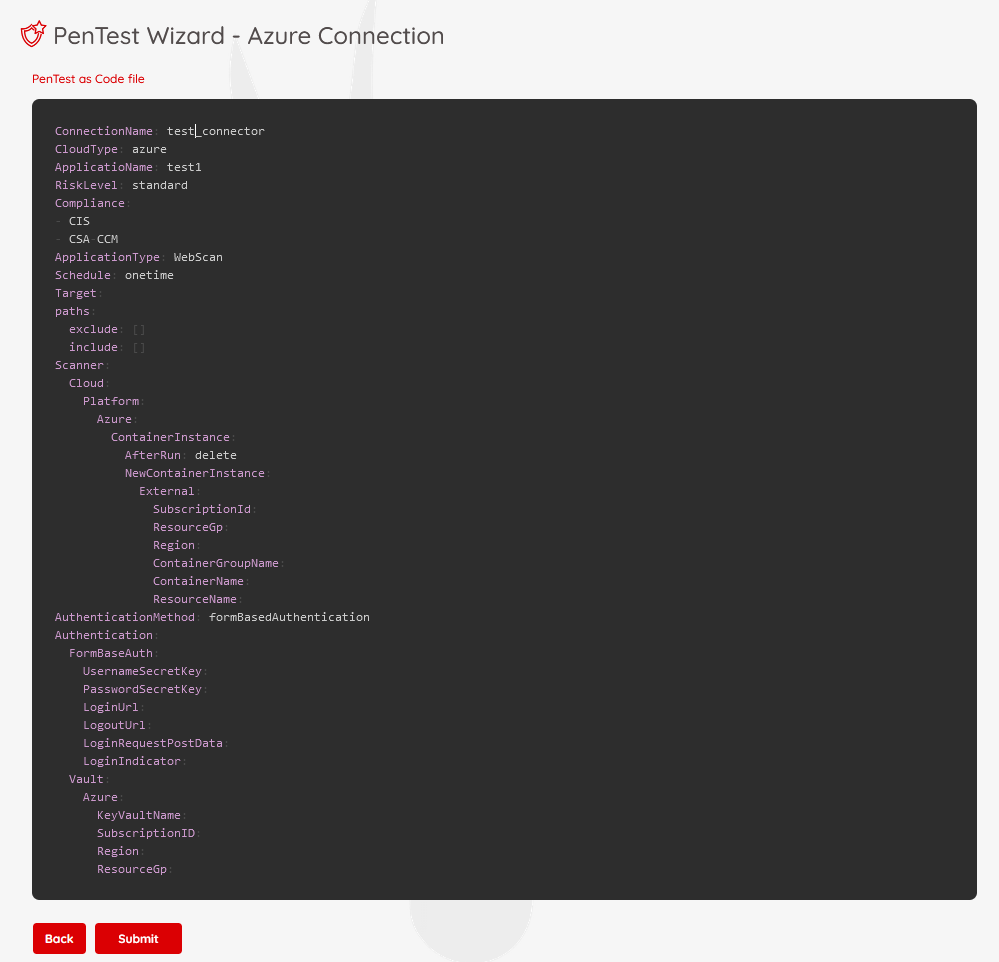
Note: To understand more about the available options in PAC file, check this page. Review all the items and if everything is fine, click on "Submit" to submit a new pentesting job to Prancer.
What happens next?
Prancer PAC engine starts to communicate with your Azure tenant, create the PAC scanner based on the configurations details in the PAC file, complete the pentesting scan, and show the results on "Pentest Findings" page.